An IP address alone is not enough to determine who performed a given action — especially in environments using DHCP, VPNs or shared devices. In such cases, identifying users based solely on network traffic is inaccurate and often leads to incorrect conclusions.
TrueID correlates IP addresses with users and devices using data from systems such as DHCP, RADIUS and Active Directory. This enables precise attribution of activity to a specific person or asset — regardless of changing addresses or locations.
During security incidents, it is critical to reconstruct user activity — when the user logged in, which IP address was used and what actions were performed. Without a consistent identity context, this process is time-consuming and error-prone.
TrueID enables session tracking and event correlation across multiple systems, allowing teams to reconstruct a complete timeline of user activity. This significantly reduces investigation time and helps identify the root cause.
Security systems often detect anomalies — suspicious traffic, unusual behavior or access attempts but without user context, it is difficult to assess the actual risk.
TrueID enriches events with identity data, providing the context needed for proper interpretation. This allows security teams to make faster decisions and respond more effectively to incidents.
User activity is distributed across multiple systems — from authentication, through application usage, to network traffic. Without a unified view, analyzing behavior and detecting anomalies becomes difficult.
TrueID connects these events into a single view, enabling full user session analysis. This helps teams better understand context and identify unusual behavior more quickly.
Organizations must demonstrate who accessed specific resources, when actions were performed and whether they complied with security policies. Fragmented data and lack of identity correlation make this difficult.
TrueID provides consistent user-to-action mapping, enabling clear audit trails. It supports compliance processes and simplifies reporting and analysis for audits.
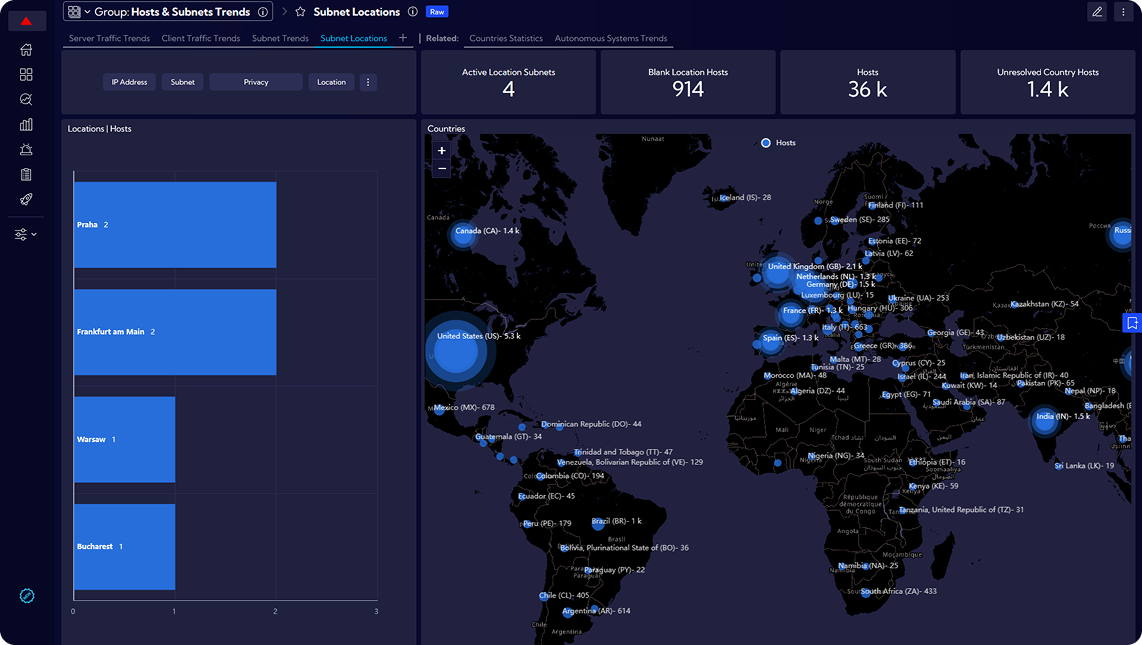
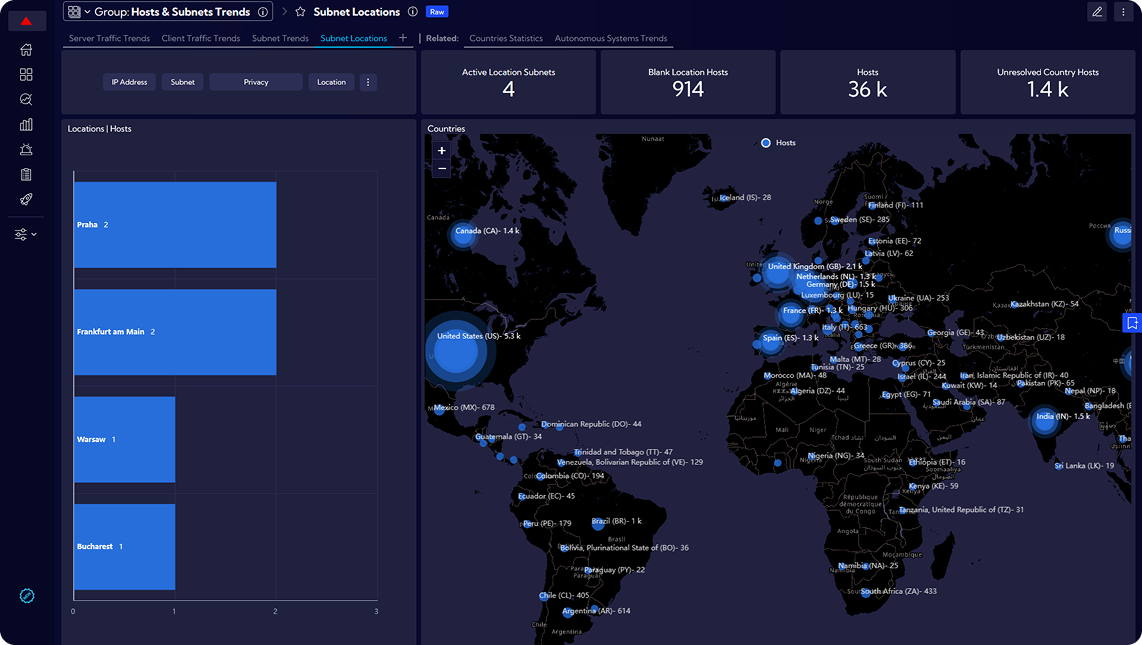
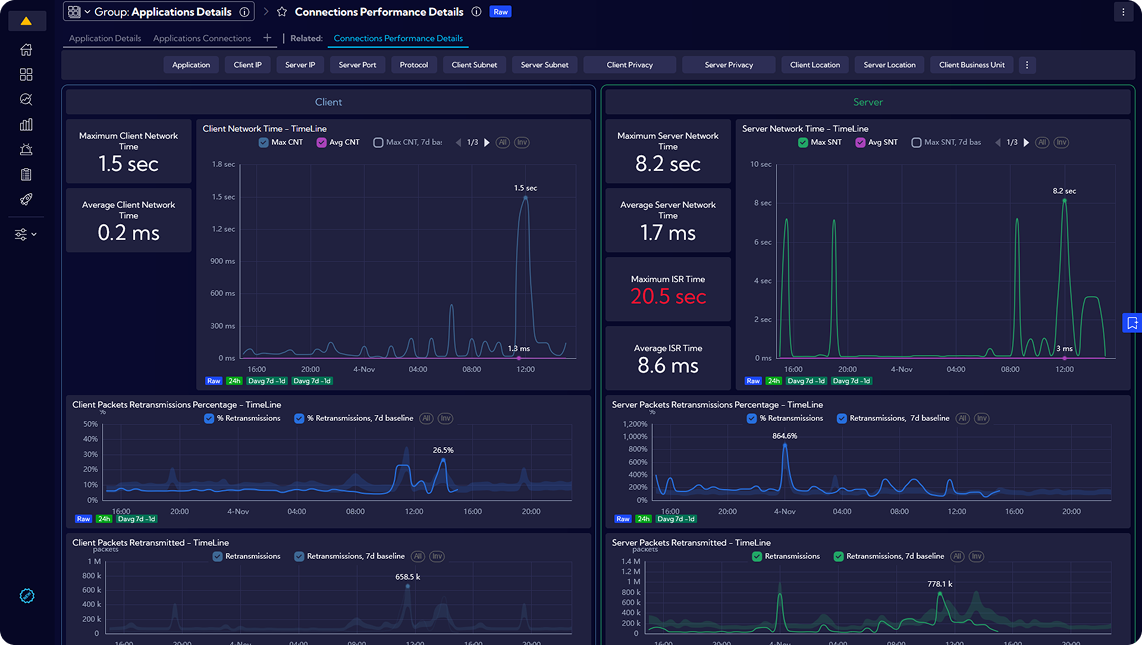
Full insight into the operation of the IT network, allowing to make quick decisions about resource allocation and actions to protect against unplanned downtime.
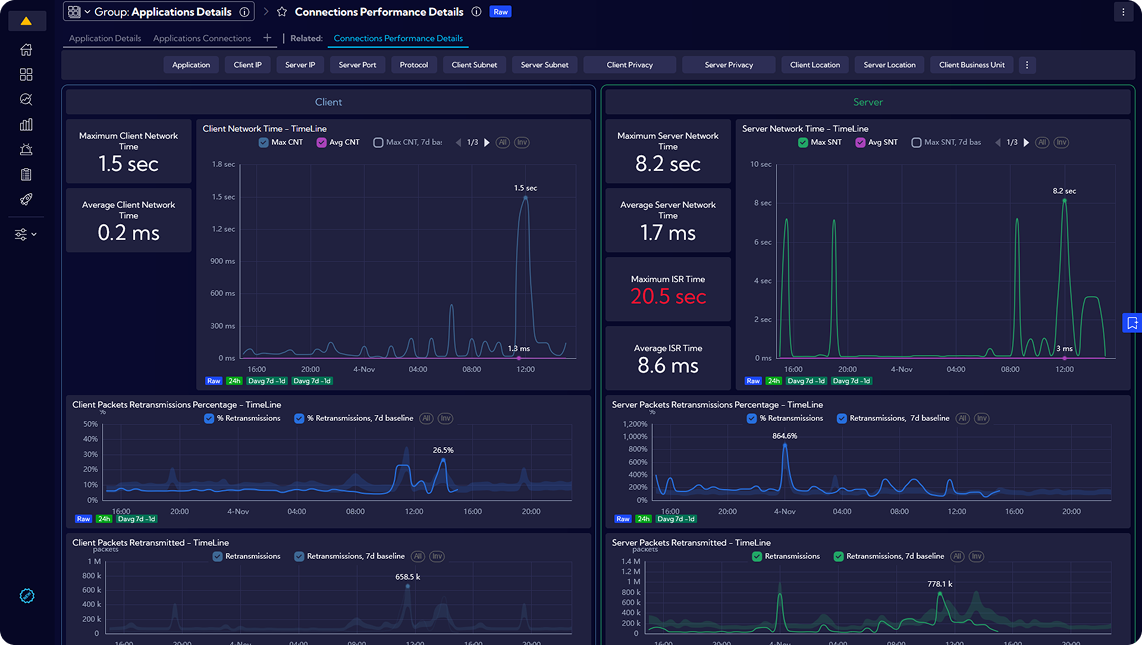
Critical performance metrics measurements in any infrastructure. Focused on L4-L7 monitoring, from TCP analytics to L7 app detection and apps response times measurements.
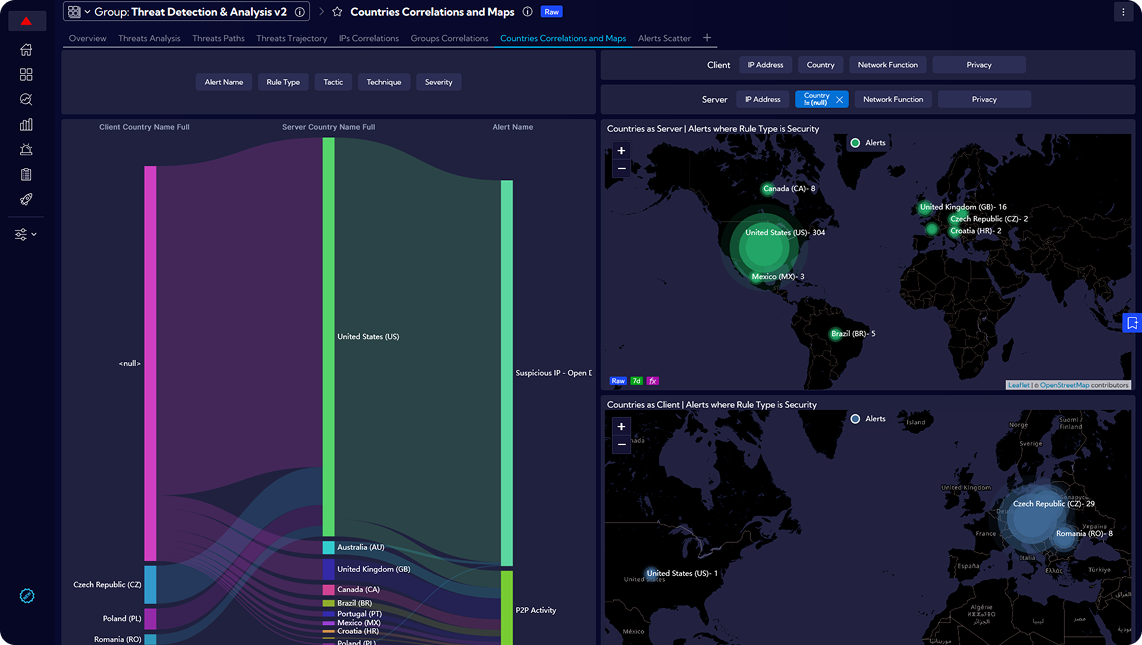
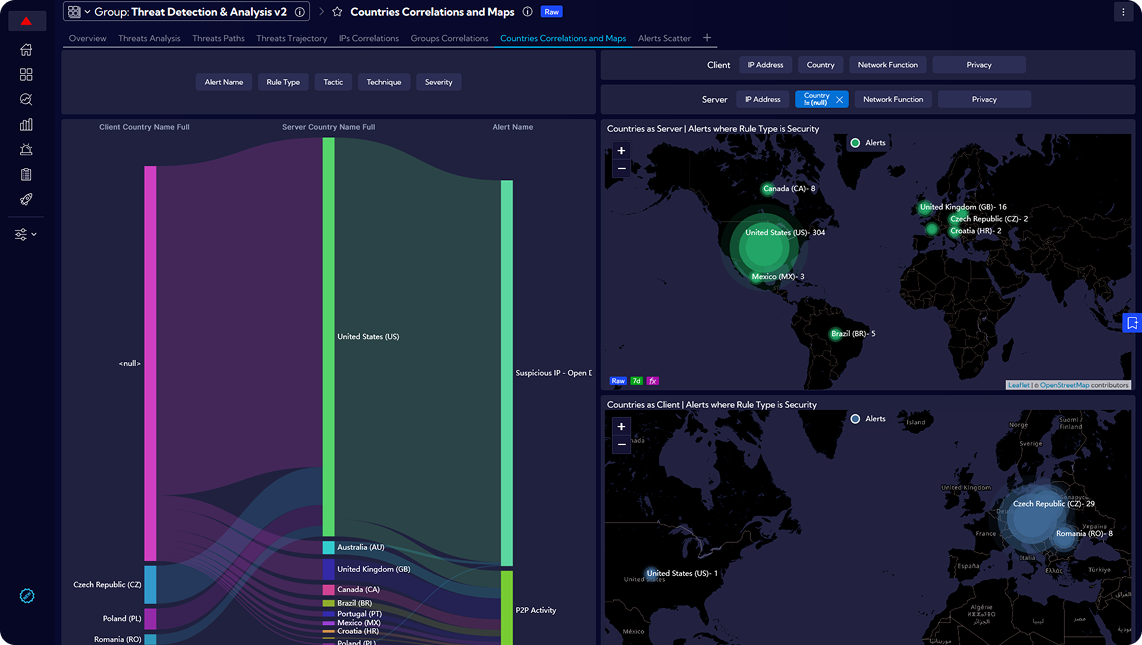
Sycope detects and analyzes security anomalies and threats across the entire organization using the MITRE ATT&CK framework. This helps identify real attacks faster and reduce the risk of breaches.
Real-time, automatic inventory tracking, monitoring devices and their associated assets using NetFlow data and dependency mapping.